A Blueprint for Building a Generic Authorization Service - Ashwin & Fletcher | BSidesSF 2026
Ashwin & Fletcher (Platform Security, Roblox) – 25 min, advanced
How Roblox built Guard, a highly available, centralized authorization control plane using Topaz and OPA to secure thousands of microservices.
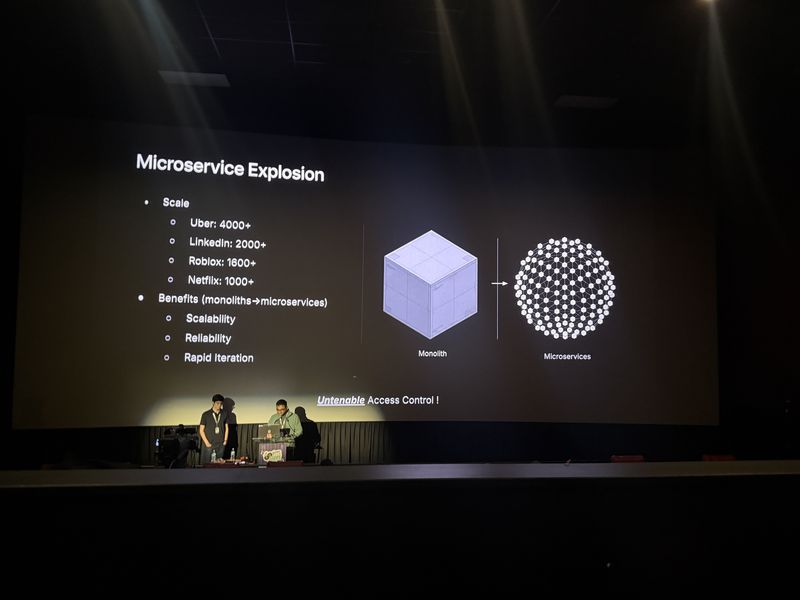
The Crisis of Fragmented Authorization
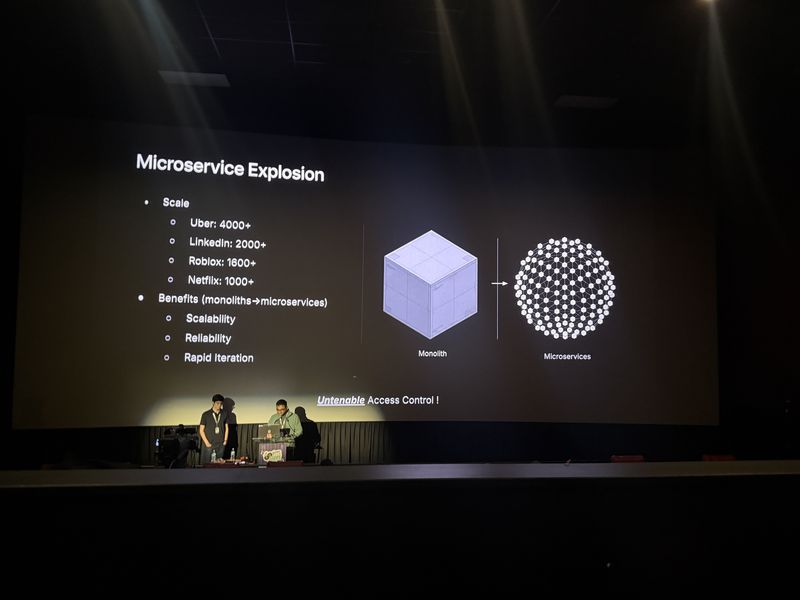
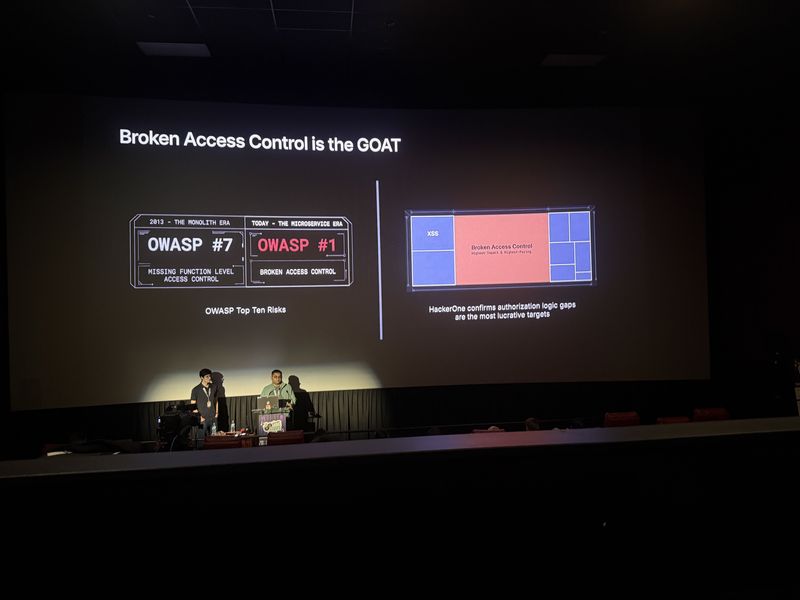
As companies scale to thousands of microservices, access control becomes decentralized and brittle. This fragmentation slows developer velocity and creates severe security blind spots, making broken access control a top vulnerability.
- Companies are running 1,000 to 4,000 microservices, leading to access control at thousands of isolated locations.
- Fragmented authorization leads to redundant logic, orphan permissions, and broad persistent access.
- Broken access control has been the #1 security vulnerability since 2021.
This spaghetti architecture doesn’t just look messy, it fundamentally slows down your developer velocity.
Every time a new authorization solution is introduced into your infrastructure, it becomes a security bottleneck.
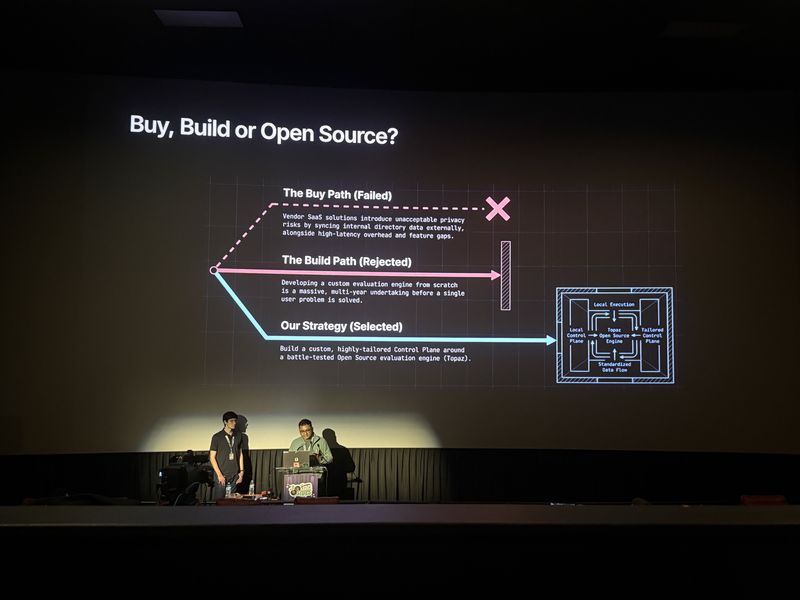
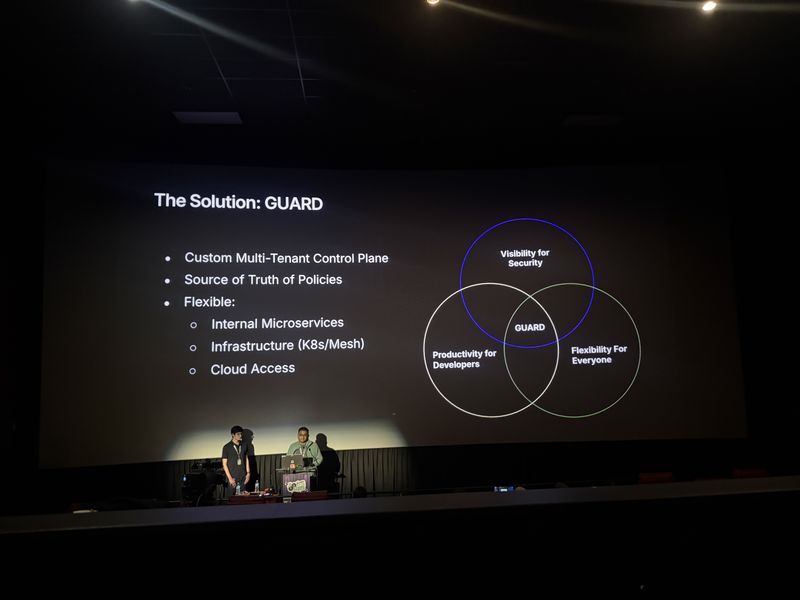
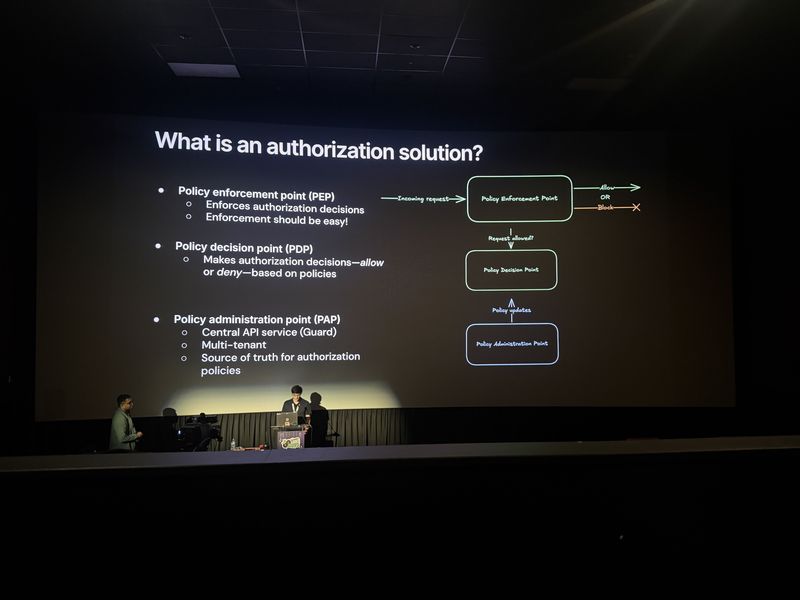
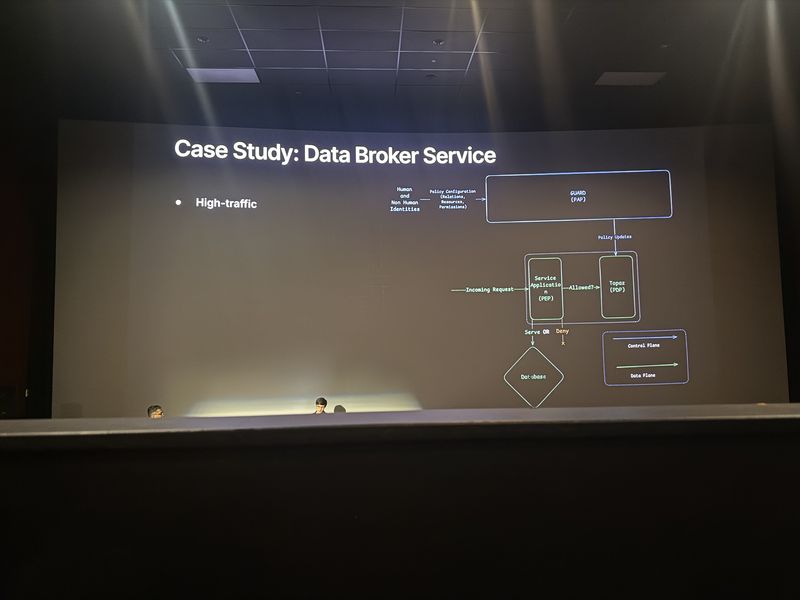
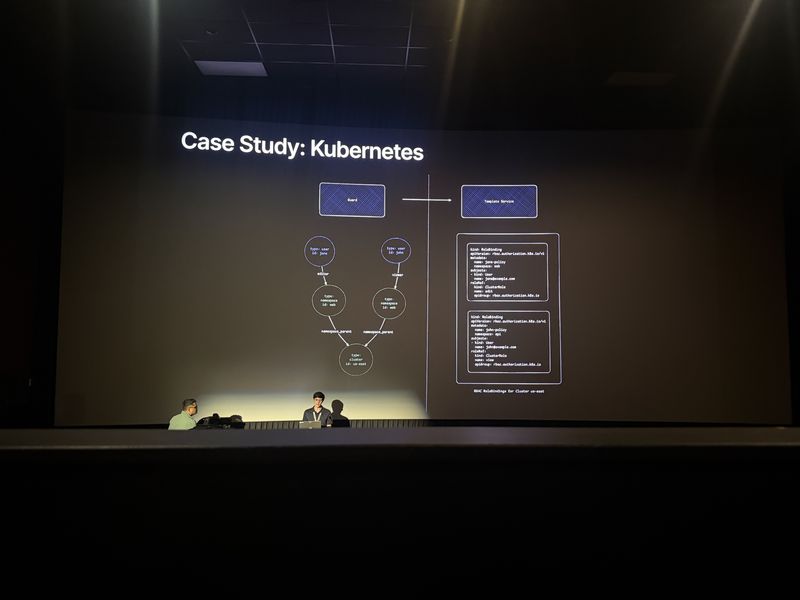
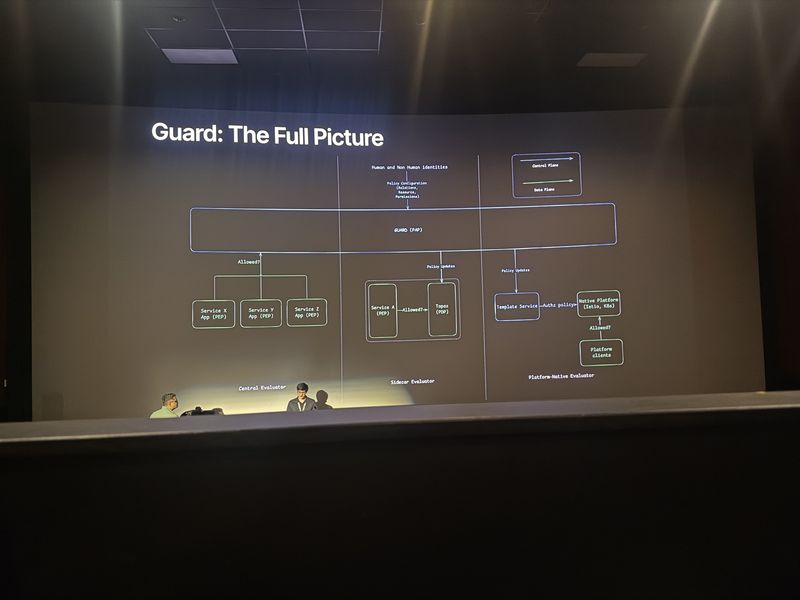
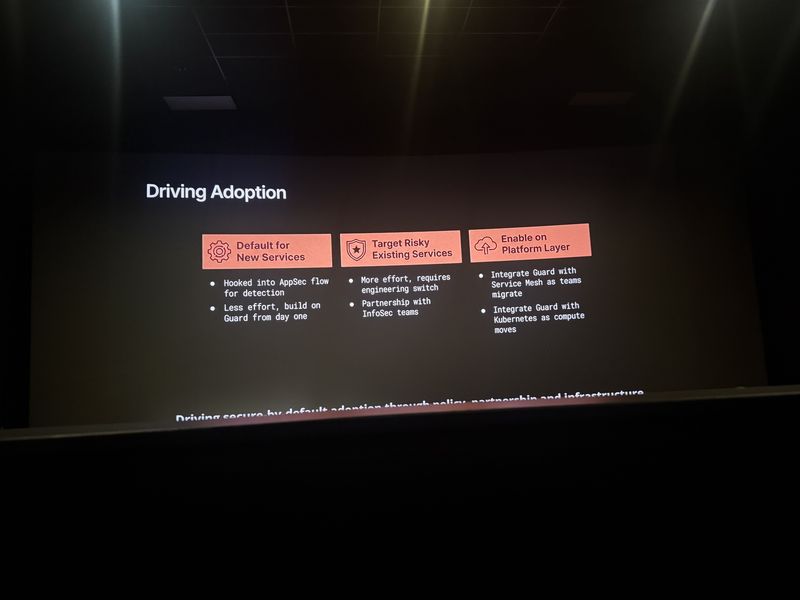
The Guard Architecture and Topaz
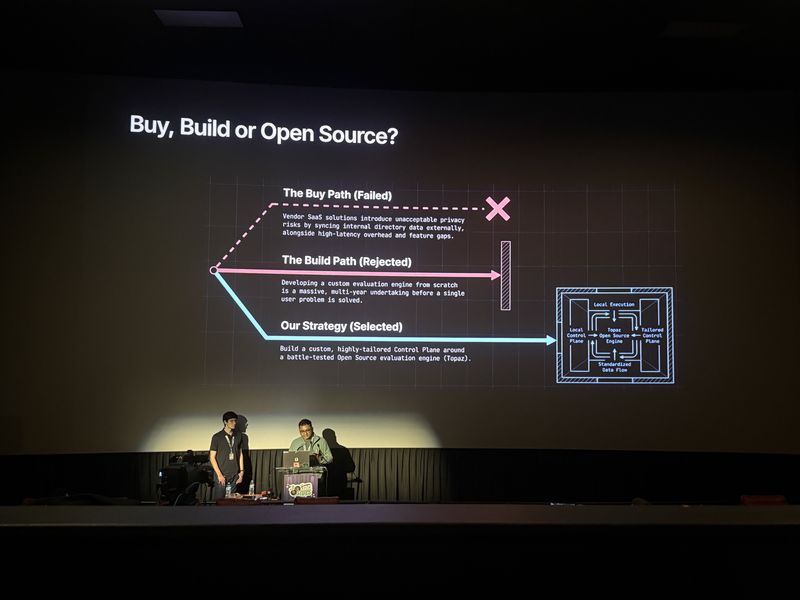
To solve fragmented authorization, Roblox built Guard, a custom multi-tenant control plane. It uses Topaz, an open-source OPA-compliant engine, deployed as a sidecar to evaluate policies locally with millisecond latency.
- Authorization must be decoupled entirely from individual application code.
- Topaz combines Open Policy Agent (OPA) for ABAC with a graph traversal engine for RBAC.
- The sidecar model ensures high availability; if the control plane goes down, the sidecar continues on last known data.
To fix this, we need to decouple authorization from individual application code entirely.
Authorization is non-optional. If you can’t authorize, then the only secure fallback is to deny everything.
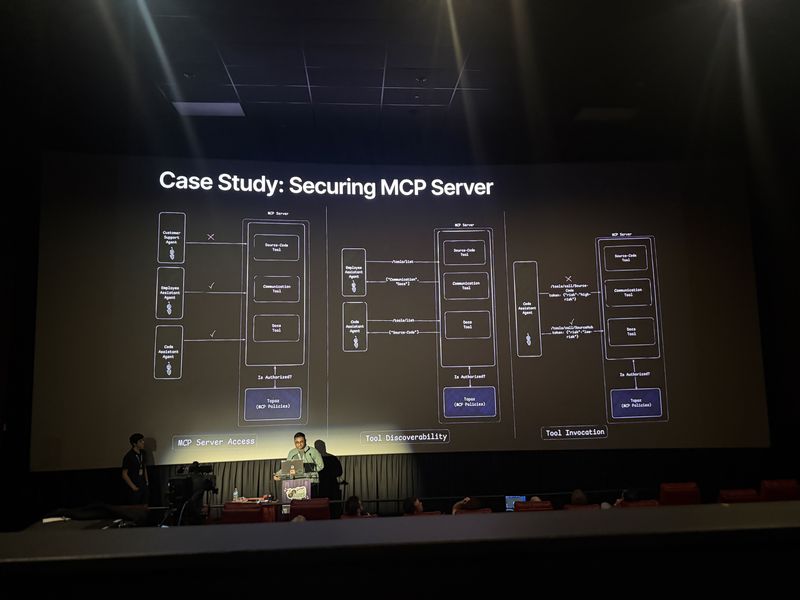
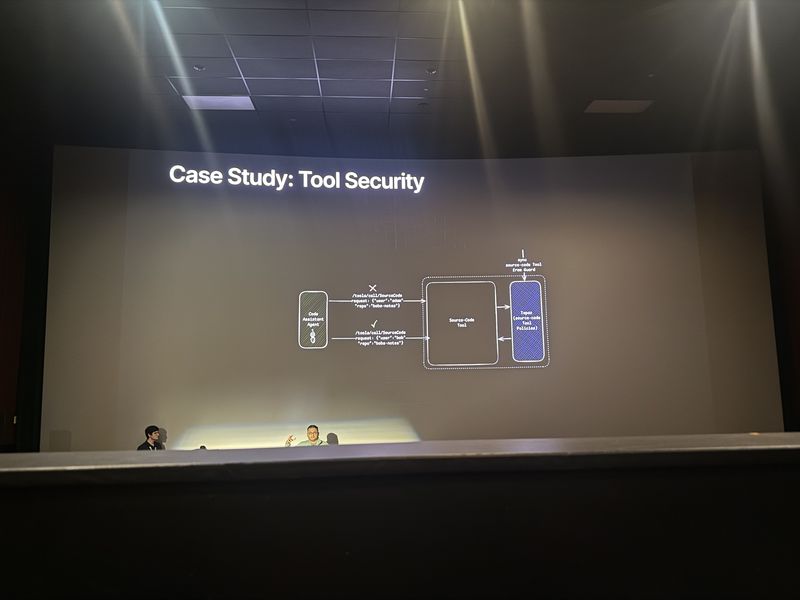
Securing AI Agents and MCP Servers
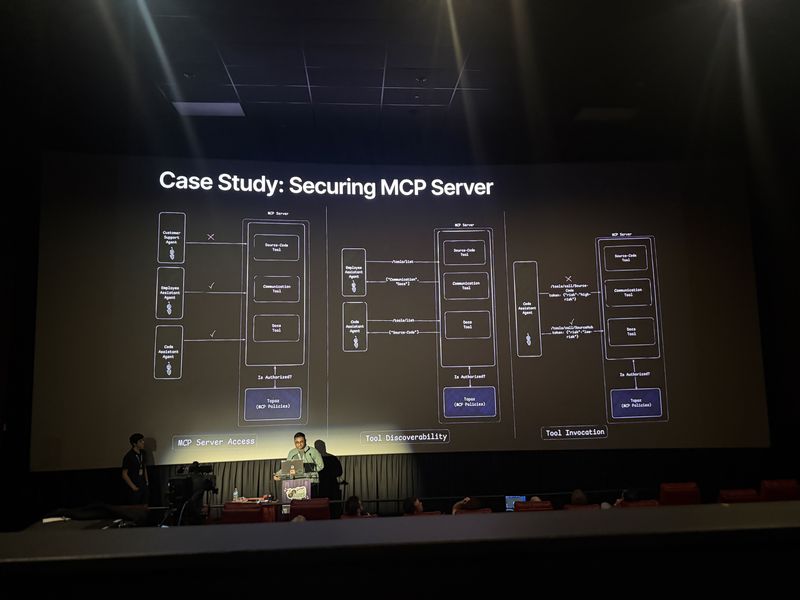
The authorization framework is identity-agnostic, making it ideal for securing Model Context Protocol (MCP) servers used by AI agents. It allows granular control over which agents can access specific tools and repositories.
- The framework secures humans, agents, and workload identities alike.
- Administrators can restrict external customer support agents from accessing internal MCP servers.
- The system enables dynamic tool discoverability and risk-score-based access control for AI agents.
You can use the same framework for securing your MCP servers as well. This framework is agnostic to what kind of identity you’re securing against.
Lessons Learned: Performance
Deploying a sidecar model revealed latency and startup challenges. The team implemented decision caching to reduce latency to microseconds and had to sequence container startups to ensure policies loaded before the application accepted traffic.
- Local network hops (1-2ms) can be too slow for critical services.
- A short-lived decision cache in the auth SDK drops latency to tens of microseconds.
- Topaz sidecars must finish their initial policy sync before the main application starts.
Local is too slow. 1 to 2 milliseconds is fast but it was a measurable latency cost to the overall service.
Technologies
OPA, Topaz, Istio, Kubernetes, Go, WebAssembly, GitHub, Model Context Protocol (MCP)
Frequently Asked Questions
What is Roblox Guard and how does it handle authorization at scale?
Guard is Roblox’s centralized, multi-tenant authorization control plane built on Topaz and OPA. It deploys as a sidecar to each microservice, evaluating policies locally with millisecond latency while maintaining high availability even if the control plane goes down.
How can OPA and Topaz be used to secure AI agents and MCP servers?
Because the authorization framework is identity-agnostic, it can enforce granular access control for humans, AI agents, and workload identities alike, including restricting which agents can access specific MCP servers, tools, and repositories.
Why is broken access control the number one security vulnerability?
As companies scale to thousands of microservices, authorization logic becomes fragmented across isolated locations, leading to redundant logic, orphan permissions, and broad persistent access that creates severe security blind spots.