Seeing the Forest Through the Trees: Risk and Threat Modeling - Sean | BSidesSF 2026
Sean, Senior Security Engineer at SoundCloud – 23 min, intermediate
How to effectively threat model, prioritize risks based on business impact, and communicate security needs to executives in monetary terms.
The Business Definition of Risk
Risk is defined by the business and its executives, usually in monetary terms. While headlines focus on zero-days, the vast majority of breaches stem from non-malicious human factors and a lack of basic controls.
- 68% of breaches are caused by non-malicious human factors.
- 98% of those incidents could have been stopped if MFA was enabled.
- Executives often prioritize risks based on headlines rather than actual exploitability.
A risk to your business is defined by your business itself. It’s defined by the executives who have an actual stake in the business.
68% of breaches are non-malicious human factors… 98% of them could have been stopped if the account that got exploited had multifactor authentication enabled.
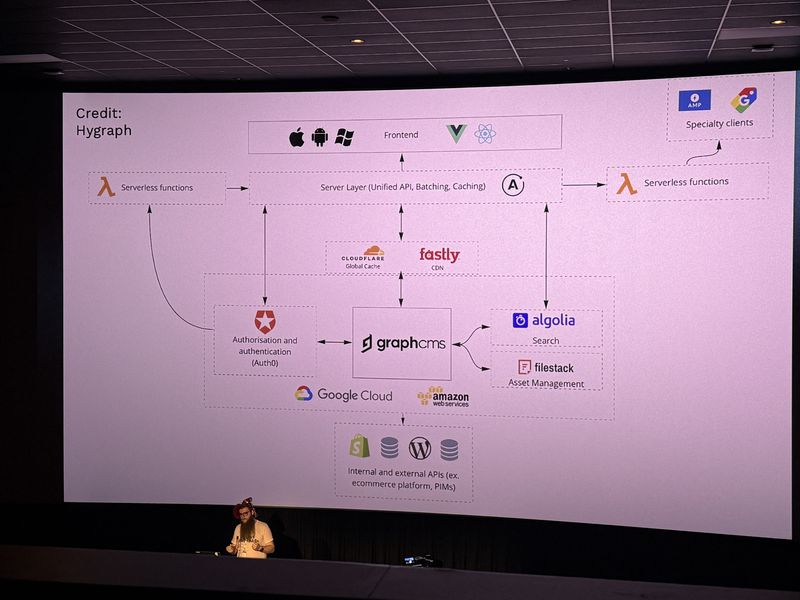
Effective Threat Modeling and Data Flow Diagrams
A solid threat model requires a complete inventory, data flow diagrams, and an understanding of business operations. Diagrams should be simple and layered to avoid overwhelming the audience.
- Map out your tech stack, how data flows across it, and what systems interconnect and why.
- Layer data flow diagrams instead of cramming everything into one unreadable chart.
- Document security questions immediately during the modeling process so context isn’t lost months later.
If there is so much information on the page that your eyes start glazing over and your audience falls asleep, you really need to peel back that data flow diagram.
You need to ensure that you write it down… in 6 months when you go back to this, you’re probably going to forget it.
Threats, Vulnerabilities, and Prioritization
A risk only exists when both a threat and a vulnerability are present. Security teams must avoid catastrophizing and focus on the likelihood and business impact of events.
- Threats are the events or actions, while vulnerabilities are the lack of controls.
- Avoid “James Bond-ing” scenarios unless you are in national security; focus on what is likely to happen.
- Prioritize based on likelihood and exploitability rather than raw CVSS scores.
Risks only exist when there is both a threat and a vulnerability because without either of those, it is not possible for that event to occur.
If you are just prioritizing things based on just raw CVSS, you are going to start drowning and just feel completely overwhelmed by the amount of vulnerabilities out there.
Communicating with Executives
To get buy-in, translate risks into monetary terms and present alternative solutions. Documenting risk acceptances and mitigations is crucial for accountability.
- Translate technical risks into monetary losses to effectively communicate with executives.
- Document the who, what, why, and when of mitigations in a single source of truth.
- Present alternative solutions if the ideal fix is too costly or time-consuming.
- Mitigation reduces likelihood or impact but doesn’t always eliminate the risk entirely.
At the end of the day, your average CEO doesn’t care if you get ransomware. They care that you’re losing a million dollars a day.
Technologies
GitHub, CrowdStrike, WAF, Auth0, Cloudflare, Google Cloud, AWS
Frequently Asked Questions
How do you communicate security risks to executives?
Translate technical risks into monetary losses and present alternative solutions with documented costs. Executives respond to dollar figures and business impact, not CVSS scores or technical jargon.
Why shouldn’t you prioritize vulnerabilities based only on CVSS scores?
Raw CVSS scores don’t account for exploitability or business context. Prioritizing by likelihood and actual business impact prevents teams from drowning in an overwhelming volume of vulnerabilities that may pose little real-world risk.
What percentage of data breaches are caused by human error?
According to the talk, 68% of breaches are caused by non-malicious human factors, and 98% of those could have been prevented if the compromised account had multi-factor authentication enabled.